advertisement
Why Diversity Is Important For A Strong Cybersecurity Team
Medicine. Aeronautics. Academia. When you’re a cybersecurity professional, the colleague next to you could have started in one of these…
Medicine. Aeronautics. Academia. When you’re a cybersecurity professional, the colleague next to you could have started in one of these industries—or just about any other you can imagine. The backgrounds of cybersecurity professionals are more diverse than those of professionals in other industries. And because cybersecurity as an industry is so new, these professionals likely didn’t study security in school either.
That includes LinkedIn’s Chief Information Security Officer (CISO) Geoff Belknap, who graduated college with a business degree. I hosted Geoff on a recent episode of Security Unlocked with Bret Arsenault to talk about strategies for recruiting cybersecurity talent and for solving the cybersecurity skills gap.
Strengthen your cybersecurity team through diversity
advertisement
Geoff, who joined LinkedIn in 2019, leads the organization’s internal security teams in building a safe, trusted, and professional platform. He brings more than 22 years of experience in network architecture and security leadership to his role at LinkedIn. He previously was the CISO at Slack, where he built the security organization from the ground up, including laying the groundwork for Slack’s production incident management process.
He earned a Bachelor of Science degree in Business Management at Western Governors University. One of his favorite things about cybersecurity is that it’s a multi-disciplinary and inter-disciplinary practice where people from different specialties, including business and other non-technical backgrounds, can contribute.
One of cybersecurity’s much-discussed biggest challenges is the skills gap. The cybersecurity industry is projected to triple year-over-year through 2022, but the shortage of cybersecurity professionals is in the millions globally, according to an article in The CyberWire1. The skills gap is caused, in part, because the industry is relatively new and people don’t receive training on how to work in cybersecurity, according to Geoff. If a company wants to interview 10 candidates with 20 years of experience for a cloud security engineer role, it could be waiting for a very long time.
advertisement
He recommends that organizations expand their idea of the right person for an open cybersecurity position. Stop thinking that the only person that is right for a role in cybersecurity majored in cybersecurity in college and that a principal-level network security cloud architect will be an expert in all three cloud platforms.
Instead, consider people who can process and analyze a collection of information, understand your company’s technology, and understand what the organization is trying to accomplish and the tools available. Inquisitive people who are passionate about problem-solving can grow into a cybersecurity position and become effective contributors to the organization. By investing in people with useful raw skills and developing their cybersecurity skills, organizations fill roles and add valuable diverse perspectives to their cybersecurity teams.
Once you fill those cybersecurity roles, retaining employees is critical. The secret to that is always company culture, Geoff said. Compassion and empathy are not only good traits to adopt but also essentials for an organization wanting to attract and retain the best talent. Authentic organizations care about their people and recognize that they need time outside work. After all, psychologically healthy people are the best asset for any organization.
advertisement
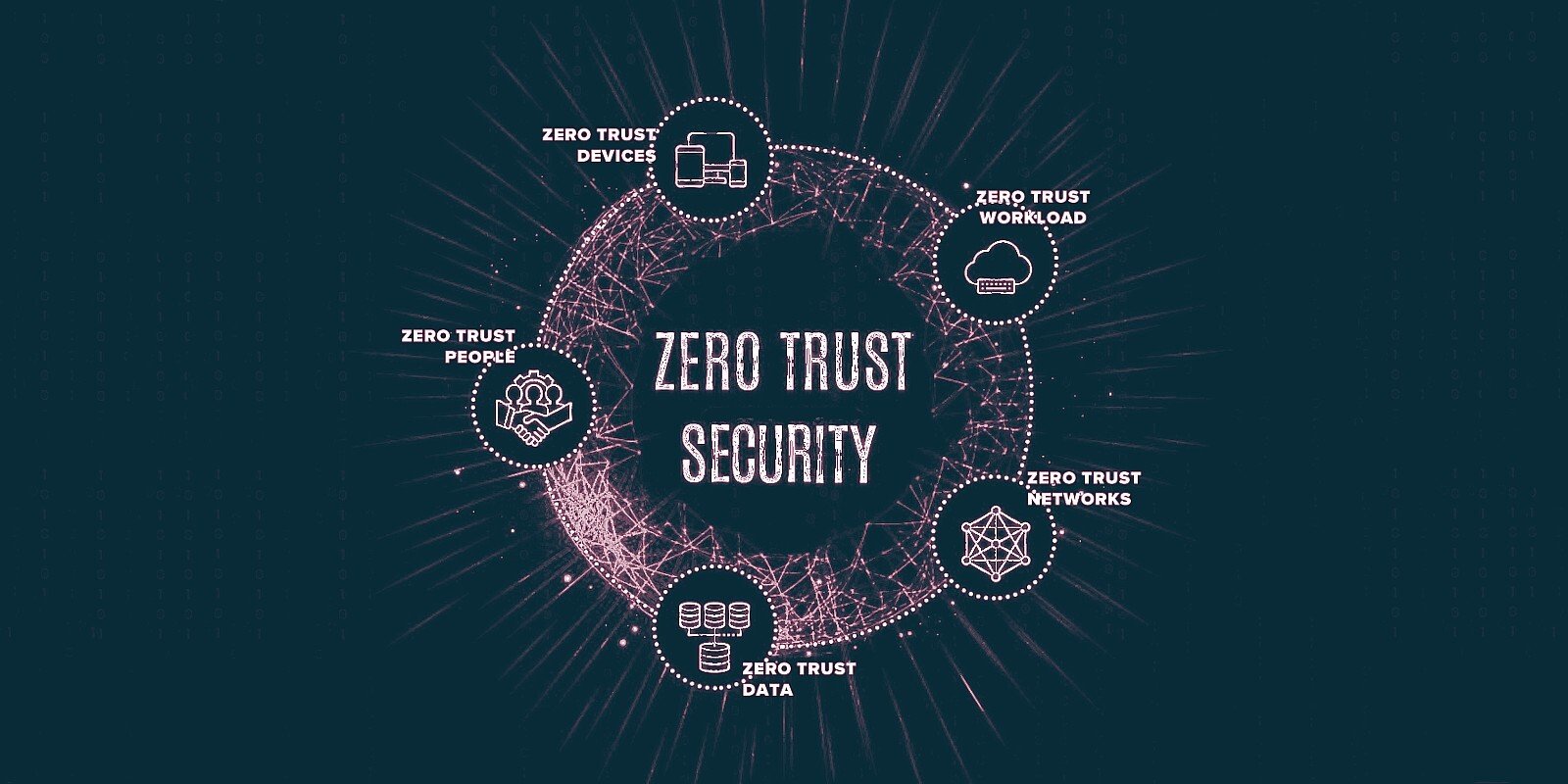
During our conversation, Geoff also shared his appreciation for the Zero Trust approach because it reinforces the idea that there is no safe haven. Security is a thought process rather than an end goal you can attain. Acknowledging that there is no castle where you can lock away your data and keep it safe makes you rethink your production environment and your risk assessment.
That’s a powerful realization because it puts you on a path to explore why things aren’t as secure as they should be, according to Geoff. To learn why he thinks cybersecurity professionals from nontraditional career paths can be especially successful in a Zero Trust environment, listen to Building a Stronger Security Team on The CyberWire.